Add a second layer of security with multi-factor authentication
Just one easy-to-guess password can stop your business in its tracks. Xero puts an extra deadbolt on the door to help keep your data secure.
What is multi-factor authentication (MFA)?
Multi-factor authentication (MFA) is an additional way of checking that it’s really you when you log in.
Adds an extra check at login
It combines something you know (your username and password) with something you have (an authentication app on your smartphone or tablet).
Helps prevent unauthorised access
The second layer of security is designed to prevent anyone but you from accessing your account even if they know your password.
Did you know?
Up to 80% of data breaches can be prevented with basic actions like enabling MFA to protect your account from attacks. (Source: DBIR, 2020)
Bad actors and organised crime
70% of breaches are caused by ‘bad actors’, with 55% of these in organised crime. (Source: 2020 Verizon Data Breach Investigations Report.)
Theft, errors and social attacks
67% of breaches are due to credential theft, errors and social attacks. (Source: 2020 Verizon Data Breach Investigations Report.)
Financial gain is the main motive
Financial gain is still the primary motive for cyberattacks. (Source: 2020 Verizon Data Breach Investigations Report.)
Global cost of data breaches
The global average cost of data breaches reported in a 2019 report was US$3.9 million. (Source: Security Intelligence)
Use Xero Verify for fast authentication
Xero Verify is the only authenticator app that sends push notifications when you log in to Xero.
Other way to authenticate your account
You can also use Google Authenticator or FreeOTP, but you won’t receive push notifications; you’ll need to enter a code instead.
No smartphone or tablet?
If you don’t have a smartphone or tablet, you can use WinAuth.
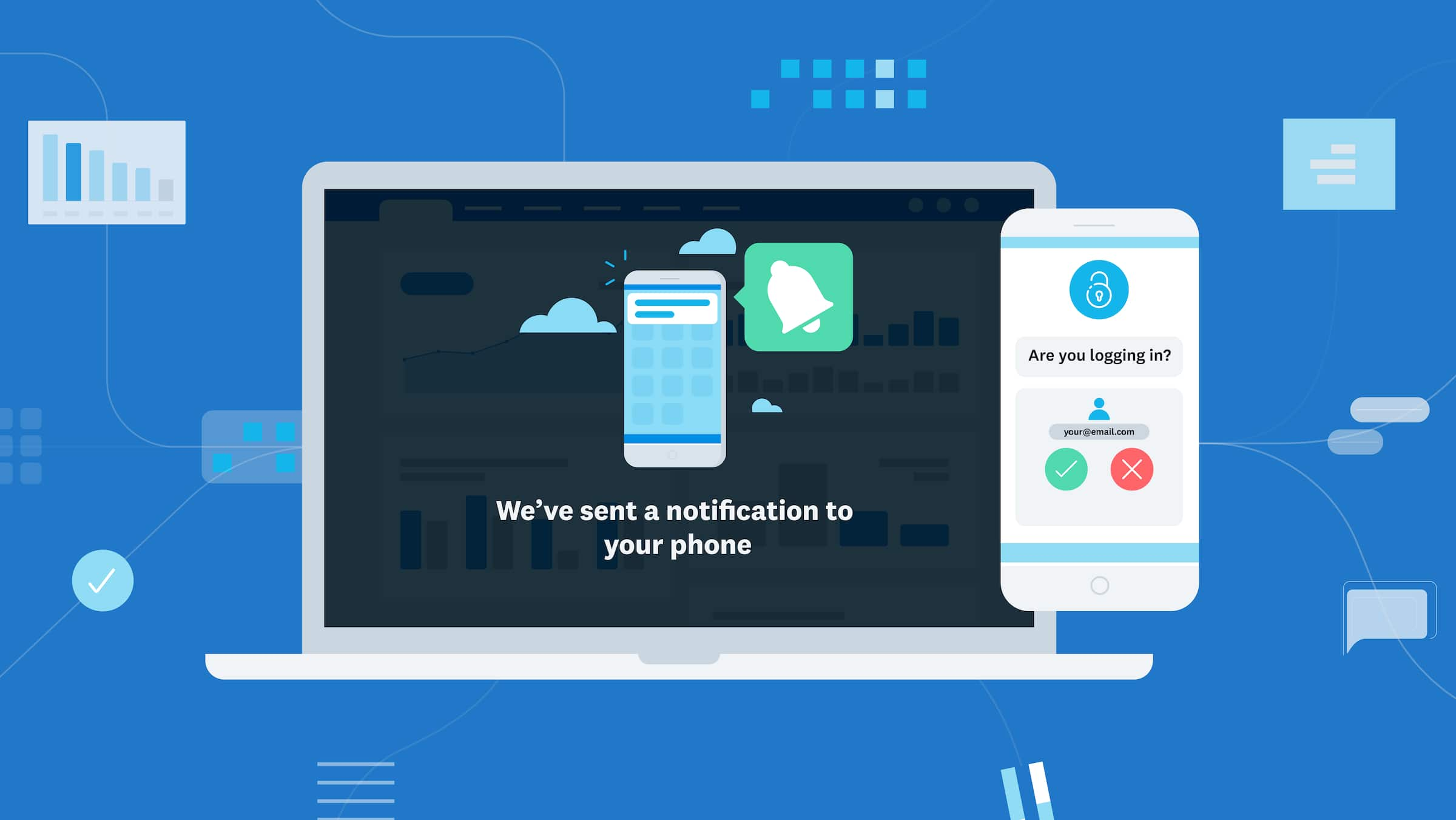
Receive push notifications from Xero Verify
When you use the Xero Verify app to authenticate your account, you’ll receive push notifications when you log in to Xero.
Step 1: Download Xero Verify
Xero Verify sends push notifications when you log in to Xero. Download Xero Verify from the Apple or Google app store.
Apple App StoreGoogle Play app storeStep 2: Sync the app with Xero
Follow these steps for setting up MFA to see how to sync Xero Verify to your Xero login (or watch the videos listed below).
Steps for setting up multi-factor authenticationStep 3: Logging in to Xero
Enter your email and password as usual. Xero Verify immediately sends a notification to your mobile device. Approve it and you’re all set.
Log in to Xero now
Watch the videos on setting up MFA
If you’re not asked to set up MFA when you log in to Xero, you can set it up yourself. The videos below walk you through the steps.
Setting up MFA when you log in to Xero
In Xero, click your initials or image; click Account; under Multi-factor authentication, select Set up, then follow the instructions.
Multi-factor authentication for securityHow to set up Xero VerifyHow to set up Google Authenticator
Additional ways to secure your data
Good practice for keeping you personal data secure
Keep your data safe by following these tips.
- Have a backup email address in case you don’t have your phone handy or need another way to verify who you are
- Keep your software, including the apps on your phone and tablet, up to date
- Keep your login details to yourself; if you invite others into Xero or a client file, they need their own login and MFA
- Use strong, unique, private passwords (not your cat’s name!) on all accounts including your backup email address
- Using the same password across different accounts introduces additional vulnerabilities that you have no control over
- Enable MFA on all your online accounts
Want more info on MFA and security?
Blog post and support articles
Read a blog post and Xero Central support articles about multi-factor authentication.
Why we’re mandating multi-factor authentication globally (Blog)Setting up multi-factor authenticationHow to log in to XeroTroubleshoot multi-factor authenticationUse multi-factor authentication on a new device